GravityZone Business Security Premium /GravityZone Elite
Endpoint Security solution with harden defenses, reduce risk, and analyze threat landscape
Talk to us
Want to buy Bitdefender GravityZone Business Security Premium /GravityZone Elite? Or Interested in training? Call us..
Table of Contents
- 1 GravityZone Business Security Premium /GravityZone Elite
- 1.1 What is Bitdefender GravityZone Business Security Premium /GravityZone Elite?
- 1.2 Bitdefender GravityZone Business Security Premium / GravityZone Elite distributor / dealer in India.
- 1.3 Bitdefender GravityZone Business Security Premium / GravityZone Elite Supported Operating Systems
- 1.4 Bitdefender GravityZone Business Security Premium / GravityZone Elite Supported Virtual Machine
- 1.5 Bitdefender GravityZone Business Security Premium / GravityZone Elite Minimum Hardware Requirements
- 1.6 Bitdefender GravityZone Business Security Premium / GravityZone Elite help with installation
- 1.7 Bitdefender GravityZone Business Security Premium / GravityZone Elite Features List
What is Bitdefender GravityZone Business Security Premium /GravityZone Elite?
GravityZone Business Security Premium /GravityZone Elite’s antivirus and cyber security solutions safeguards organisations from cyber attacks, advanced persistent threats (APTs) and ransomware using machine-learning-driven security technologies.Easy to manage from a single console, the solution covers physical, virtual, mobile, and cloud-based endpoints and email.With low overhead it provides the necessary visibility and control required .
Bitdefender GravityZone Business Security Premium / GravityZone Elite distributor / dealer in India.
Factonity Systems Pvt Ltd is an authorised distributor / dealer / reseller of Bitdefender GravityZone Business Security Premium / GravityZone Elite products in India. We manage the import compliances of the software and sell in India in Indian currency.
Please contact us to:
- Request a pricing information / quotation.
- Retail purchase as a consumer in INR
- Corporate purchase order in INR, as we are an India based vendor.
- Get GST complaint tax invoice with input credit in India.
- Local technical support / training and demo of Bitdefender GravityZone Business Security Premium / GravityZone Elite products
Bitdefender GravityZone Business Security Premium / GravityZone Elite Supported Operating Systems
Windows 10 November 2021 Update (21H2) Windows 10 May 2021 Update (21H1) Windows 10 October 2020 Update (20H2), Windows 10 May 2020 Update (20H1), Windows 10 November 2019 Update (19H2), Windows 10 May 2019 Update (19H1), Windows 10 October 2018 Update (Redstone 5), Windows 10 April 2018 Update (Redstone 4), Windows 10 Fall Creators Update (Redstone 3), Windows 10 Creators Update (Redstone 2), Windows 10 Anniversary Update (Redstone 1), Windows 10 November Update (Threshold 2), Windows 10 (RTM, version 1507), Windows 8.1, Windows 8, Windows 7
Ubuntu 14.04 LTS or higher, Red Hat Enterprise Linux / CentOS 6.0 or higher, SUSE Linux Enterprise Server 11 SP4 or higher, OpenSUSE Leap 42.x, Fedora 25 or higher, Debian 8.0 or higher, Oracle Linux 6.3 or higher, Amazon Linux AMI 2016.09 or higher
macOS Monterey (12.x) macOS Big Sur (11.x), macOS Catalina (10.15), macOS Mojave (10.14), macOS High Sierra (10.13), macOS Sierra (10.12)
Windows 10 IoT Enterprise, Windows Embedded 8.1 Industry, Windows Embedded 8 Standard, Windows Embedded Standard 7, Windows Embedded Compact 7, Windows Embedded POSReady 7, Windows Embedded Enterprise 7
Windows Server 2022 Windows Server 2019 Core Windows Server 2019, Windows Server 2019 Core, Windows Server 2016, Windows Server 2016 Core, Windows Server 2012 R2, Windows Server 2012, Windows Small Business Server (SBS) 2011, Windows Server 2008 R2
Bitdefender GravityZone Business Security Premium / GravityZone Elite Supported Virtual Machine
GravityZone Control Centre is delivered as a virtual appliance and is available in the following formats:
OVA (compatible with VMware vSphere, View)
XVA (compatible with Citrix XenServer, XenDesktop, VDI-in-a-Box)
VHD (compatible with Microsoft Hyper-V)
Support for other formats and virtualization platforms may be provided on request.
Bitdefender GravityZone Business Security Premium / GravityZone Elite Minimum Hardware Requirements
Minimum: 2.4 GHz single-core CPU Recommended: 1.86 GHz or faster Intel Xeon multi-core CPU
Memory: Minimum free RAM: 512 MB Recommended free RAM: 1 GB HDD space: 1.5 GB of free hard-disk space
Bitdefender GravityZone Business Security Premium / GravityZone Elite help with installation
Configuring and installing the GravityZone Business Security solution is extremely simple no advanced IT security knowledge is needed. Download our quick start guide for both cloud and on-premises installations to get started with a free trial .
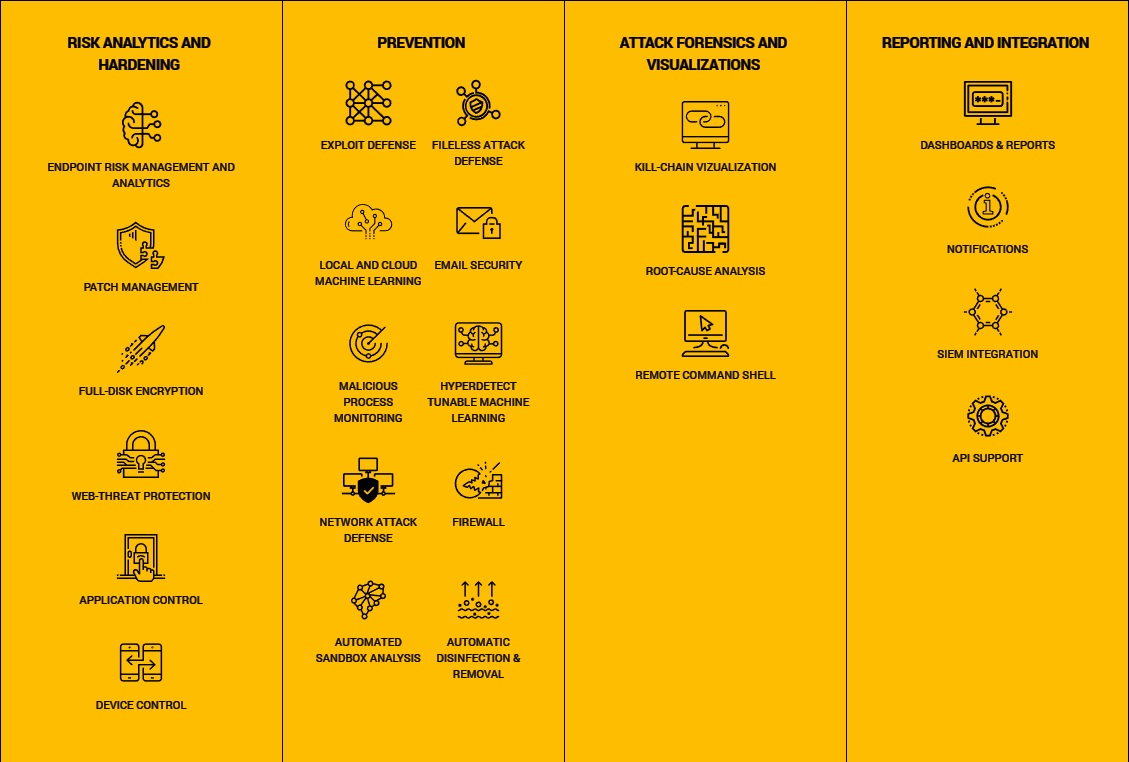
Bitdefender GravityZone Business Security Premium / GravityZone Elite Features List
- Analyze endpoint risks
- Detect misconfigurations
- Remedy vulnerabilities
- Security risk from insecure websites
- Poor Password management
- Compromised USB usage
- Cyber kill chain
- Mapping defenses
- Automatic, up-to-date tamperproof backup copies of user files
- Fileless Attack Defense
- Network Attack Defense
- Advanced Anti-Exploit
- Machine Learning Anti-Malware
- Multiple detection layers
- Process inspection
- Registry monitoring
- Code inspection
- Hyper Detect
- Risk mitigation
- Identify user actions and behaviors
- Tracking unencrypted web pages logging
- Poor password management
- Usage of compromised USBs
Behavior analysis
Integrated sandbox
Device hardening
Layered protection
- Attack forensics and visualization of organization’s threat landscape
- VulnerableEndpoints
- Zero in on specific threats
- Corrective action.
- Detect & prevent network vulnerability attacks
- Blocks brute force
- Password stealers
- Lateral movement